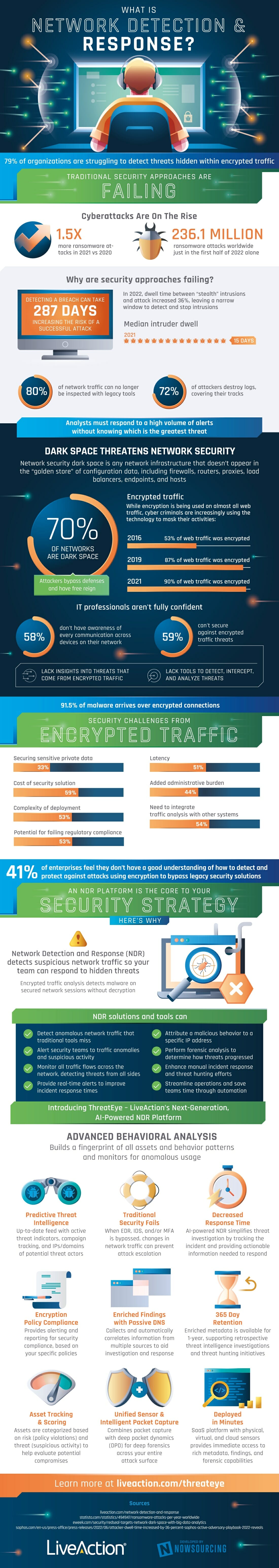
About 80% of organizations are struggling to uncover threats hidden within encrypted traffic, especially with traditional security approaches being less effective. Cyberattacks are on the rise with 1.5 times more ransomware attacks occurring in 2021 versus 2020 and 236,1 million ransomware attacks happening worldwide in the beginning of 2022. Yet why are security approaches failing?
Network Detection And Response
In 2022, dwell time between “stealth” intrusions and attacks increased by 36%, leaving very little time to detect and stop intrusions. In fact, detecting a breach can take almost 287 days, increasing the risk of a successful attack.
Q4 2022 hedge fund letters, conferences and more
80% of network traffic can no longer be inspected with legacy tools, and 72% of attackers are able to destroy logs, covering their tracks. As a result, analysts must respond to a huge number of alerts without knowing which is the greatest threat.
Network security dark space is any network infrastructure that doesn’t appear in the “golden store” of configuration data. Though encryption is being used on almost all web traffic, cyber criminals are starting to use the technology to mask their own activities.
53% of web traffic was encrypted in 2016 compared to 90% of web traffic being encrypted in 2021. Currently 70% of networks are dark spaces where attackers can bypass defenses and have free reign.
Unfortunately, IT professionals aren’t confident in stopping attackers as 58% of them don’t have awareness of every device communication on their network and 59% can’t defend themselves against encrypted traffic threats. This means that IT professionals don’t have the right tools to detect, intercept, and analyze threats or enough insight into encrypted traffic threats to put up a strong fight.
91.5% of malware arrives over encrypted connections as encrypted traffic can come with its own challenges, such as latency and the need to integrate traffic analysis with other systems. 41% of enterprises aren’t confident in their understanding of how to detect and protect against attacks using encryption to bypass legacy security solutions.
However, a Network Detection and Response (NDR) platform can be vital in updating your security strategy. This is because NDR detects suspicious network traffic so you can quickly respond to hidden threats.
NDR solutions and tools can do things like detect anomalous network traffic that traditional tools miss, alert security teams to traffic anomalies and suspicious activity, provide real-time alerts to improve incident response times, and more so you can be protected in the modern age.
Infographic source: Live Action