The typical perception of someone who spends their days in and out on a computer crunching binary code, is our typical stereotype of a hacker. In our minds it probably falls somewhere along the lines of an adult male who lives in his mother’s basement, subsisting on energy drinks and his computer screen tan. However, when it comes to literally cracking the code on hacking, many have turned to a seemingly incongruous comparison: sports.
Q1 2021 hedge fund letters, conferences and more
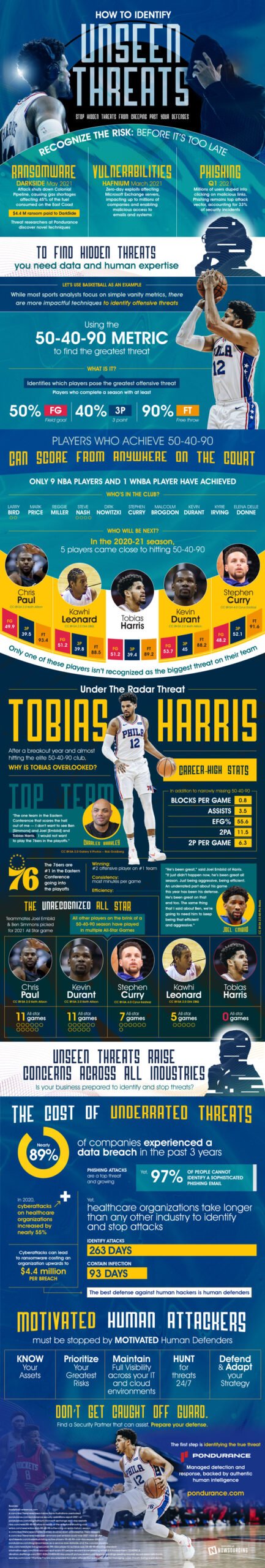
In order to identify offensive strikes basketball players typically use a ration of 50-40-90. This metric has become increasingly important when trying to target the source of an offensive attack. In basketball this could be anything from three pointers to alley-oops. This metric helps identify which players pose the greatest threat to the opposing team.
Simply broken down, any player who competes at a professional level of 50% field goals, 40% three pointers and 90% free throws, are players that pose the largest tactical threat. More than one of these players on one team could mean a massive advantage that could actually be unfair to the other team.
Secure Yourself From Unseen Threats
However, the good news for avid sports fans is that only 9 players in NBA history have met this metric. WIth names in the category like Larry Bird and Stephen Curry, you really have to be extraordinary to be a statically speaking “triple threat.” But, that doesn’t mean that these teams are out of the woods just yet.
In the 2020-2021 season alone five players almost hit this metric. Known as "unseen threats," these players are where the data world has taken an interest. Unknown targets are the biggest threat in the industry. Recently these sorts of attacks have been aimed at hospitals and healthcare branches. This is potentially catastrophic for the medical community. If we cannot find enough data to create specific metrics for identification, then we could allow for a security disaster.
There are steps that can be taken to make ourselves more secure. Knowing what type of data is out there is very important to knowing how to secure it. In order to defend you must know what you are defending. Additionally, you must be willing to adapt to changes in order to protect yourself and your data. This is becoming increasingly more important as we move through our digital age into the future. By ensuring our privacy we can help to secure our future.
Learn how to find the unseen threats before it’s too late: