Did you know that the word “virus” is derived from the Latin word for “poison”?
How Viruses Work
A virus is not the same thing as bacteria. It is much smaller and not technically an organism. Composed of only genetic material and protein, viruses need living hosts to survive. They can easily spread from person to person by touch or through microscopic water droplets in the air, such as from an uncovered sneeze or cough.
[REITs]Q3 hedge fund letters, conference, scoops etc
The most alarming aspect of viruses is that one miniscule virus in your body can multiply exponentially and make you very sick. Once it enters your system, it infiltrates your healthy cells. It will inject its genetic material to hijack your cells so that it can make copies to infect other cells. This is how viral diseases work, such as the flu.
How Computer Viruses Are Similar to Pathogens
There is a reason that some malware has been coined a “virus”. A computer virus is a small bit of software (or genetic material) that rides on computer programs. Every time the program is active, the virus is able to attach to other programs (like an uncovered sneeze).
For example, an email virus can disguise itself as a normal email attachment. When clicked or simply opened, the virus launches itself to your contacts. It continues this pattern with subsequent victims, becoming an epidemic.
Other Malicious Software
Viruses aren’t the only software that put our cybersecurity at risk. Trojan horses and worms are also common insidious programs.
Trojan horse computer programs cause damage and replicate automatically under the guise of a normal program, such as a game. Worms are standalone pieces of software that travel through security defects, or holes, replicating along the way.
Best Defense Against Malware
When it comes to fighting viruses, prevention is the best method. The problem is that viruses come in many shapes and forms. After getting sick or vaccinated, your body’s cells can only protect against what they know. For example, if the virus you contract is a slightly different strain from the one used in your flu shot, you will still get sick with influenza. Even the smallest alterations can be enough to outwit your white blood cells.
Likewise, protecting your data is becoming increasingly hard with the sheer number of cyberattacks. What’s more, the rapid technological innovation yields not only an augment but diversification in malware.
Why Does Cybersecurity Matter?
Data breaches have the potential to put millions of people at risk. To specify, personal information (home address, credit card information, social security number, etc.) could be released for anyone to access. This could lead to crimes such as fraud or identity theft.
Equifax, MySpace, Yahoo, and a variety of other platforms have suffered significant cyberattacks. To put it in perspective, Yahoo’s data breach affected all of its users’ accounts – an amount near 3 billion. This is a prime example of why a proactive cybersecurity plan is crucial, especially with regard to large businesses.
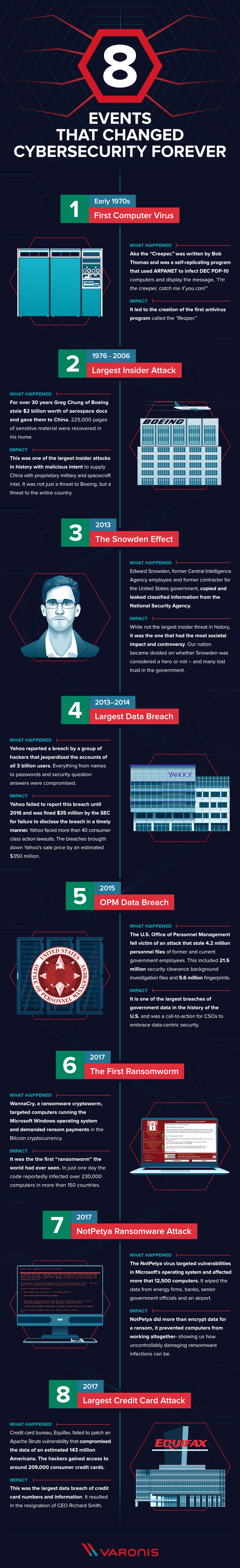
8 Pivotal Cyberattacks
Varonis composed a list of 8 events that changed cybersecurity forever. While they represent a small fraction of the total amount of cyberattacks, the scope of the events remind us why it’s necessary to dedicate resources to online security. A little malware and/or data leak can involve millions of people and dollars in addition to putting the nation at stake.
- The First Computer Virus
In the early 1970s, a self-replicating program called the “Creeper” used the Internet’s precursor, ARPANET, to infect computers. A message appeared that read, “I’m the creeper, catch me if you can!” This inspired the creation of the first antivirus program with the fitting name “Reaper”.
- The Largest Insider Attack
The largest insider attack in history comes from Greg Chung of Boeing. From around 1976 to 2006, Chung supplied China with sensitive military and spacecraft intel, amounting to $2 billion. His actions were of a national scope, threatening America as a whole.
- The Snowden Effect
As a former Central Intelligence Agency and government employee, Edward Snowden was able to leak classified information from the National Security Agency. While Greg Chung is still attributed for the largest insider attack in history, Snowden’s threat had the largest direct impact on society. His controversial actions divided the nation.
- Largest Data Breach
As mentioned earlier, Yahoo’s data breach jeopardized 3 billion accounts with the release of names, passwords, security questions, etc. Though this happened in 2013, Yahoo didn’t officially report the breach until 2016. They faced a $35 million fine, lawsuits, and decrease in sale price by an estimated $350 million.
- Office of Personnel Management Data Breach
One of the largest breaches in government data, the U.S. OPM suffered an extensive data breach — 21.5 million security clearance background investigation files and 5.6 million fingerprints were compromised. Chief Security Officers finally realized the significance of cybersecurity.
- The First Ransomworm
Not so long ago in 2017, the first ransomware cryptoworm (or “ransomworm”) demanded bitcoin ransom payments from Microsoft Windows users. This introduced the ransomworm to the world and showed its capabilities. Over 230,000 computers in 150 countries were infected in one day.
- NotPetya Ransomware Attack
About a year ago this virus erased the hard drives of energy firms, banks, senior government officials, and an airport. It targeted Microsoft’s OS and reached nearly 13,000 computers. NotPetya prevented computers from working at all, proving the danger of modern ransomware.
- Largest Credit Card Attack
The third cyberattack in 2017, Equifax overlooked a vulnerability that affected 143 million Americans. Hackers obtained information from over 200,000 credit cards. In fact, this attack was so monumental that the CEO resigned.
Main Takeaway
As you can see, cybersecurity is not a topic to be taken lightly. The escalation of cyberattacks is evident as three increasingly overwhelming attacks occurred in 2017. What does this mean for the future of digital security? Only time will tell.
Be careful what you put online and take measures to ensure your data is secure.