Introduction to expanded password
We are witnessing a critical turning point in the history of identity assurance – departure from the time-honored seals, autographs and textual passwords.
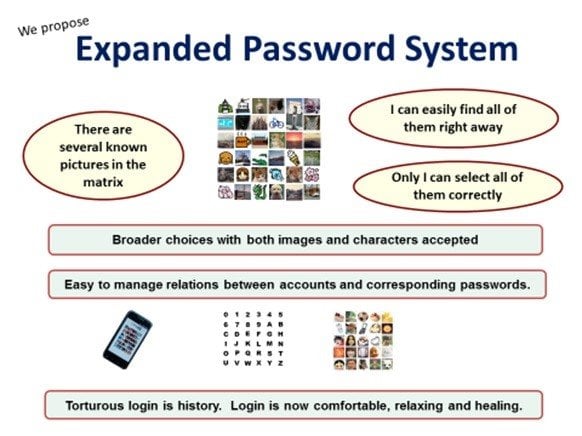
The worst part of the global password predicament will melt away when people are offered a broader password choice. Expanded Password System that we advocate accepts images as well as texts and brings an identity authentication that is secure and yet stress-free. It is being recognized by an increasing number of identity and security professionals and is now in the stage of ‘Draft Proposal’ of OASIS Open Projects.
Q4 hedge fund letters, conference, scoops etc
However, quite a few people seem to pay little attention to this inevitable evolvement, presumably because they are trapped in two major misbeliefs – (1) a ‘password-less’ (volition-less) authentication is desirable and (2) biometrics is displacing the password.
I have repeatedly referred to these misbeliefs in my earlier articles - “’Weak Panel’ And Weak Lock/Key System’ Of‘ Weak Door’” and “Four Puzzling Issues of Identity Authentication”. gist of which was that volition-less authentication is not compatible with the values of democracy and that it is logically obvious (1) that biometrics has to depend on another factor as a fallback means against false rejection, (2) that the password/PIN is mostly used as the fallback means in cyberspace and (3) that the biometrics and the fallback password/PIN are deployed in "multi-entrance" method (as against "multi-layer" method that brings up security) that brings down the security the password/PIN has so far provided.
I have recently noticed that one important point has been missing in my earlier writings. It was the lack of quantitative examination of the exactly opposite security effects of multiple authenticators deployed in ‘multi-entrance method as against ‘multi-layer’ deployment.
Horrific Difference between ‘Multi-Entrance’ and ‘Multi-Layer’ Deployments
It appears that there are so many security professionals who are indifferent to the exactly opposite security effects of 'multi-layer' and 'multi-entrance deployments, presumably because they wrongly took it for granted that security improves more or less automatically where multiple authenticators are deployed, because they see multiple factors there. ‘2’ always looks larger than ‘1’ if the context is ignored.
‘Multi-Layer’ is also represented by ‘In-Series’, ‘In-Addition-To’, ‘All/BothAnd’ and ‘Conjunction’, while ‘Multi-Entrance’ by ‘In-Parallel’, ‘In-Stead-Of’, ‘EitherOr’ and ‘Disjunction’. I would like to take this opportunity to offer a quantitative examination of multiple authenticators deployed in these two distinctly different methods.
Vulnerability (attack surface) of an authenticator is generally presented as a figure between 0 and 1. The larger the figure is, the larger the attack surface is, i.e., the more vulnerable. Assume, for instance, as just a thought experiment, that the vulnerability of the PKI-enabled token (x) be 1/10,000 and that of the password (y) be 10 times more vulnerable, say. 1/1,000. When the two are deployed in ‘multi-layer’ method, the total vulnerability (attack surface) is the product of the two, say, (x) and (y) multiplied. The figure of 1/10,000,000 means it is 1,000 times more secure than (x) alone.
On the other hand, if the two are deployed in ‘multi-entrance’ method, the total vulnerability (attack surface) is obtained by (x) + (y) – (xy), approximately 0.0011. It is about 11 times less secure than (x) alone.
So long as the figures are below 1, whatever figures are given to (x) and (y), deployment of 2 authenticators in ‘multi-layer’ method brings higher security while ‘multi-entrance’ deployment brings lower security. As such ‘multi-layer’ and ‘multi-entrance’ must be distinctly separated when talking about security effects of multiple authenticators.
Well, the calculation “(x) + (y) – (xy) had already appeared in this video “Biometrics in Cyber Space – ‘below-one’ factor authentication” published some years ago, though without a detailed explanation of why (xy) was deducted from the sum of (x)+(y). Here is the answer: when (x) and (y) is very small, the (xy) is extremely close to 0, which we can practically ignore, but we should not ignore it when the figures are considerably large.
Suppose a case that the two authenticators are deployed in such an extremely careless manner, for instance, that the attack surfaces of (x) and (y) reach 70% (0.7) and 60% (0.6) respectively. If simply added, the sum would be 130% (1.3). It conflicts with the starting proposition of the vulnerability figure being between 0 and 1.
Imagine an all-white surface area. Painting 70% of it in black leaves 30% white surface. Painting 60% of the remaining 30% in black will result in 88% black and 12% white surfaces. Painting 60% first in black and then painting 70% of the remaining 40% brings the same result of 88% black and 12% white. x + y(1-x) = y + x(1-y) = x + y - xy The overall vulnerability (attack surface) is 0.88 (88%) in this case.
The same calculation applies to biometrics used in cyber space where it has to rely on a fallback password/PIN deployed in ‘multi-entrance’ method against false rejection. (The meaning of false rejection is discussed with graphs in the article “Unnecessary Deaths Presumably Brought By Biometrics Misunderstood )
You might assume that biometrics deployed with a password/PIN in ‘multi-layer’ method should bring us a very high security. But, very sadly, this scenario never comes true. When rejected by biometrics, what can we do? We will only see that we are unable to login even if we can feed our password/PIN.
In a media report “AI May Soon Defeat Biometric Security, Even Facial Recognition Software”, AI is taken up as a major threat to biometrics security. But, we do not need to wait for AI. Biometrics is already defeated by itself.
Biometrics vendors may be able to make their products more fake-proof, but even the perfectly fake-proof biometrics would still be less secure than a password where it is used together with a fallback password; as mentioned earlier, two entrances placed in parallel provide nice convenience not only to consumers but also to criminals, say, lower security.
Nevertheless more and more consumers are reportedly adopting biometrics, fingerprints and selfies in particular, assumedly because
(a) consumers reckon that placing a finger on a sensor and taking a selfie are much simpler and easier than feeding PIN/passwords, and
(b) consumers are not informed that the password/PIN that they had registered are deployed in ‘multi-entrance’ method with biometrics, which brings down the security to the level lower than a password/PIN-only login.
Consumers would have reacted very differently to biometrics if they had been correctly informed of its true security effects. While informed consent must be respected, misinformed consent must be corrected, particularly when it brings a serious case of false sense of security (illusion of safety). Biometrics vendors are urged to explicitly tell consumers that biometrics is a tool to improve convenience, not security, and must be used with a yet stronger password where they do not like to ruin the security that the passwords/PIN have so far provided.
Transition to Expanded Password System
Now, the overall picture may well be much clearer to the reader. Firstly, it is obvious that we have to depart from text-only password systems. Secondly, we are aware that we have to get rid of the bad dream of ‘password-less’ security. Thirdly, we know that biometrics is not a security-enhancing tool in cyberspace.
And yet we need some form of authentication method that does not get completed without our knowledge or against our will/volition. Here we see the transition from Text-only Passwords to Expanded Password System that provides us with a far broader password choice.
Expanded Password System has such desirable features as follows.
- It is not only stress-free for users but fun to use, as opposed to the dread and overhead that come today with creating, memorizing and storing passwords
- It turns a low-entropy password into high-entropy authentication data
- It eases the burden of managing the relationship between accounts and passwords
- It deters phishing attacks
- It can be deployed under any type of circumstance, including combat and panicky emergency
- It supports existing schemes, such as:
- Biometrics which require passwords as a fallback means against false rejection
- Two/multi-factor authentications that require passwords as one of the factors
- ID Federations such as password managers and single-sign-on services that require passwords as the master-password
- Simple pictorial/emoji-passwords and patterns-on-grid that can be deployed on this platform.
- It is relevant whenever text passwords and pin numbers are in use
- And, nothing would be lost for people who want to keep using text passwords
- Last but not least, it continues to rely on free will/volition.
Known technical programs related to digital identity, for instance, OAuth 2/3, OpenID Connect, FIDO 2, eIDAS and so on, are all complementary to Expanded Password System.
I would also like to add that Expanded Password System can be flexibly implemented in various ways. If packaged as an ‘image-to-text converter’, it can be most easily incorporated into the existing textual password systems.
Key Takeaways
- The password predicament will not go away until the password system gets expanded to offer a broader password choice.
- Don't be trapped in the myth of "password-less" authentication. Volition-less authentication could bring us into a 1984-like Dystopia.
- Don't be trapped in the false sense of security (illusion of safety) brought by biometrics used in 'multi-entrance' method with a fallback password/PIN
- Watch what is happening with Expanded Password System and help with it where possible.
President at Mnemonic Security, Inc.
Hitoshi Kokumai
About Author:
Advocate of 'Identity Assurance by Our Own Volition and Memory', Hitoshi Kokumai is the inventor of Expanded Password System that enables people to make use of episodic image memories for intuitive and secure identity authentication. He has kept raising the issue of wrong usage of biometrics and the false sense of security it brings for 17 years.
Mnemonic Security Inc. was founded in 2001 by Hitoshi Kokumai for promoting Expanded Password System. Following the pilotscale operations in Japan, it is seeking to set up the global headquarters.
Appendix - Draft Specification of Expanded Password System
Below is the specification of Expanded Password System proposed at OASIS Open Projects.
- The system should enable the user to select any numbers of images through an interface of their choice, using a matrix of images which could be small or large depending on the level of security the user wants to achieve for the particular application.
- The system should enable the user to register a set of any numbers of images of their choice either by permutation or combination as credentials and embed them onto a matrix of images made of meaningless decoy images.
- The system should enable the user to register textual passwords by accepting characters (alphanumeric, emoji, characters of any language like Chinese, Japanese, Hindi, Arabic, etc.) as images and the system should handle all of them the same way as images.
- The system should allocate an image identifier, which is made of reasonably long random data, to each image so that the total sum of the identifiers of registered images will make the long random credential data.
- The credential data to be stored should always be hashed with a salt that is unique to each user by the latest cryptographic modules like ‘bcrypt’.
- The system should provide the user with explanations on the merits and demerits of permutation and combination for registration of images.
- The system should provide the user with suggestions on what kinds of images to register and avoid registering.