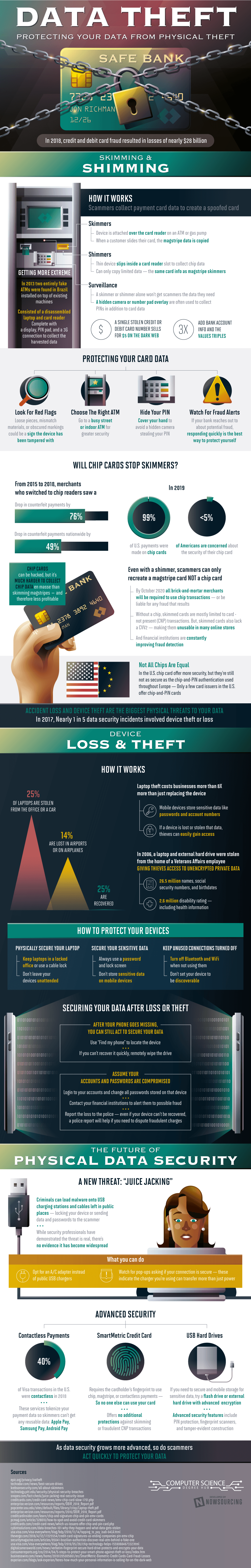
Device theft and accidental loss pose the biggest physical threats to your personal data. In 2017, nearly 1 in 5 data security incidents involved device theft or loss. In the following year, debit and credit card fraud caused nearly $28 billion in losses. Although chip cards can’t stop skimmers, merchants who switched to chip readers saw a 76% drop in counterfeit payments from 2015 to 2018. By 2020, all brick-and-mortar merchants will be legally bound to use chip transactions – or be liable for any consumer fraud that happens. Meanwhile, financial institutions are constantly improving their fraud detection programs and algorithms.
Q4 2019 hedge fund letters, conferences and more
Scammers can obtain credit or debit card information in multiple ways, most commonly by skimming and shimming.
Attaching a device over an ATM or gas pump’s card reader is known as skimming. When a customer slides their card into the machine, the magstripe data is copied, or “skimmed.” On the other hand, slipping a thin device inside a card reader slot to collect chip data is known as shimming. However, shimmers can only copy a limited amount of data… the same card information as magstripe skimmers have the ability to collect.
Data and device theft
Surveillance plays a major role in skimming and shimming technique as well since scammers can’t possibly collect all the consumer data they need by themselves. Surveillance is typically incorporated through use of hidden cameras. For example, a hidden camera or number pad overlay is often used to collect personal identification numbers (PINs) in addition to magstripe and chip data.
With this data, scammers typically sell on the black market. One stolen credit or debit card number goes for $5 USD on the Dark Web. Upon providing the bank account information associated with the card, the value triples to $15 USD.
Moving on, device loss and theft can be of equal threat to your personal data as skimming and shimming are. Physically securing not only your data, but also your devices and network information can shield you from theft- take extra precautions when traveling with your technology. 25% of laptops are stolen from the office or car, 14% are lost in airplanes or in airports, but only 25% go on to be recovered.
For example, the laptop and external hard drive from the home of a Veterans Affairs employee was stolen in 2006. This gave thieves access to: 26.5 million unencrypted names, birthdates, and social security numbers, and 2.6 million disability ratings- including patient health information.
Find more information on the future of physical data security, and how to stay protected, below.